
It’s no secret that nothing is cheaper than free. This is why so many people have considered using TunnelBear as their main VPN. At first glance, TunnelBear appears to be a great, safe, and free VPN service. But there is more to the company than meets the eye. So we asked ourselves: is TunnelBear truly trustworthy? Let’s find out!
Security: What Are The Security Tools in Apps?
Like most VPNs, TunnelBear claims to protect you from the various dangers of the internet with the use of some security tools. These tools protect you from cyber-criminals and hijackers. But not everything is great as you can see in our full review.
For now, let’s look at the security tools in the apps.
Encryption Protocols
As with most VPNs these days, TunnelBear uses AES 256-bit encryption. For those who are not familiar, AES is an acronym for Advanced Encryption Standards. Many people use it to encrypt and decrypt extremely sensitive data.
This method of encryption is used by government and military organizations across the world, so you can certainly rely on it for personal use. Unfortunately, this is the only encryption protocol that TunnelBear uses.
Additional Obfuscation
TunnelBear can keep up with some of the more sophisticated VPN providers, thanks to its obfuscation feature. This feature is mainly for users who want to be as discreet as possible when browsing online.
It is also especially useful for users living under governments that are repressive and have limited internet access laws, as well as severe theft penalties for those who forgo these limits.
The TunnelBear application is well thought out, but this feature is only available to those running Windows, Android, and macOS, and must be turned on in the app’s security settings.
Always On
You can set TunnelBear to launch each time you start up your device. This feature is useful for those who don’t want to have to reconnect it on restart. However, this can lead to unnecessary memory usage and can end up slowing some machines down quite significantly.
Luckily this is an optional feature, so if you find that you are experiencing speed and efficiency problems, you may disable it.
VigilantBear aka Kill Switch
This is one of TunnelBear’s more advanced and appealing features. The VigilantBear feature (which is a Kill Switch) ensures that your data and location remain private in the short time that it takes TunnelBear to reconnect.
This feature is also designed to automatically reconnect as soon as it detects an internet connection again. This is handy if you move between WiFi networks or move out of range of a network. Unfortunately, you are unable to run the VigilantBear protocol if your computer runs a custom proxy.
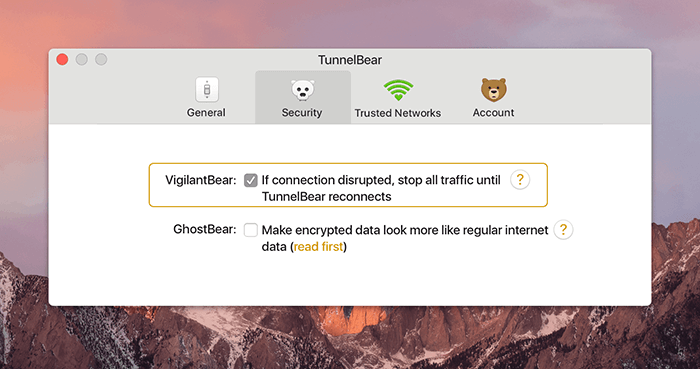
Other VPNs can sometimes be responsible for making these changes, so if you want to use VigilantBear, you will need to disable other VPNs and third-party security apps beforehand.
GhostBear
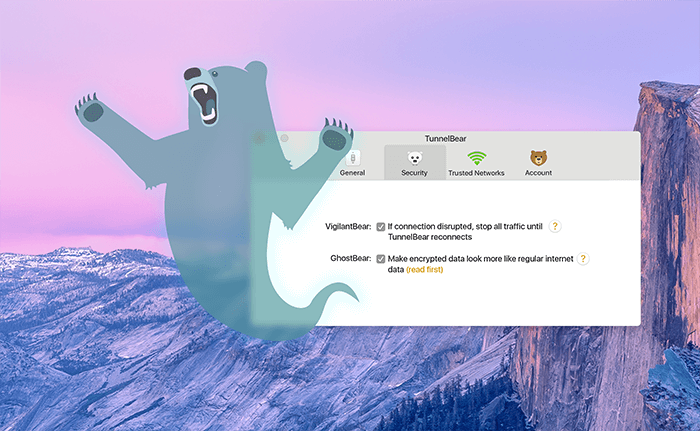
Another feature for users who value discretion over anything else is GhostBear. It makes your encrypted data less detectable to businesses, governments, and ISPs. The VPN tunnels your traffic to make it undetectable on your network.
This, in turn, makes it much more difficult to block.
Unfortunately, GhostBear is not available for iOS.
TunnelBear’s Privacy Policy: The Most Important Security Criterion
Of course, one of the biggest concerns that most people have when using a VPN is what the service provider does with the personal information they collect if they collect any at all.
TunnelBear does collect some of their users’ personal data, and even discloses a portion to third parties.
When you create or update your TunnelBear account, they collect this data and store it as ‘Account Data’. This data consists of your email address, optional Twitter ID, whether or not you are a paid user, and if so, when your subscription expires.
‘Operational Data’ is stored as well, and TunnelBear claims that this data is required to operate their services.
Is that really safe?
It is collected and stored when you connect to their network and includes things like your OS version, your TunnelBear app version, were you active this month, how much data you used this month, and events like account creation and payments made.
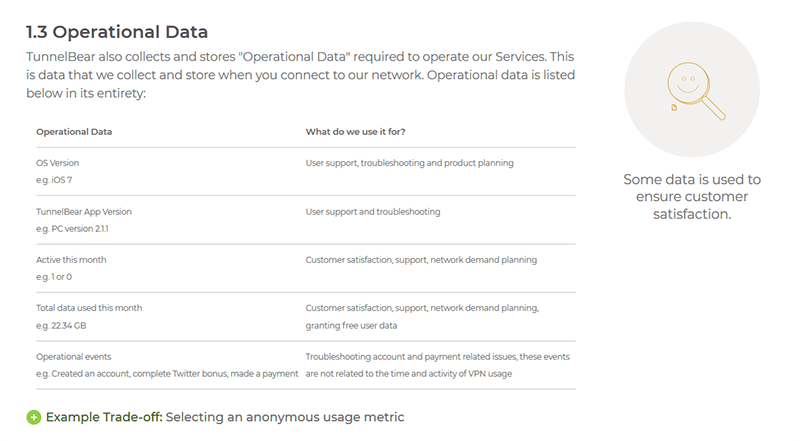
Screenshot of the “no-log” policy
The VPN collects your personal and financial data when you make payment. The company also processes your credit card information through PayPal and Stripe. This data includes the last name of the cardholder, the date that the card was used, and the last four numbers on the card.
TunnelBear also states in its Privacy Policy that it may send data to third-party service providers. This includes things such as customer support and email.
If TunnelBear is ever served with a valid warrant, subpoena, or other legal documents, and any applicable law requires the company to comply, the extent of their disclosure is limited to the Personal Data that we have mentioned above.
External Audit
TunnelBear has actually completed several independent security audits and was one of the first VPNs to do so. TunnelBear is still one of the only VPN providers in the world to complete a public end-to-end independent security audit.
This is a boost for the trust of the company’s users. And this is one of the main reasons that people are drawn to TunnelBear.
Statement from TunnelBear about the third party audit they did with Cure53
Conclusion: TunnelBear Can’t Be Trusted
While many people want to like TunnelBear for a few reasons, the cons sadly outweigh the pros. The VPN does not provide many security features, at least not as many as some of the top VPNs like ExpressVPN.
Although they do offer 256-bit AES encryption and a kill switch, TunnelBear’s other auxiliary security protocols are just not good enough. GhostBear is an excellent unique feature.
But it is not compatible with iOS. And there are a few other VPNs with similar features that also offer more platform compatibility.
VigilantBear is also one of TunnelBear’s unique features but that is definitely not enough. Despite all this, it is still considered one of the best free VPNs at the moment, as it has some great offerings. But we still highly recommend the safest VPN out there, ExpressVPN,
More information about ExpressVPN service >

Flo is the founder of the-bestvpn.com. Really concerned about security on internet, he decided to create this website in order to help everyone find the best VPN. He’s got a Business School background and now is 100% dedicated to keeping his website alive.





